
Getty Images
Researchers have unearthed never-before-seen malware that hackers from North Korea have been using to surreptitiously read and download email and attachments from infected users’ Gmail and AOL accounts.
The malware, dubbed SHARPEXT by researchers from security firm Volexity, uses clever means to install a browser extension for the Chrome and Edge browsers, Volexity reported in a blog post. The extension can’t be detected by the email services, and since the browser has already been authenticated using any multifactor authentication protections in place, this increasingly popular security measure plays no role in reining in the account compromise.
The malware has been in use for “well over a year,” Volexity said, and is the work of a hacking group the company tracks as SharpTongue. The group is sponsored by North Korea’s government and overlaps with a group tracked as Kimsuky by other researchers. SHARPEXT is targeting organizations in the US, Europe, and South Korea that work on nuclear weapons and other issues North Korea deems important to its national security.
Volexity President Steven Adair said in an email that the extension gets installed “by way of spear phishing and social engineering where the victim is fooled into opening a malicious document. Previously we have seen DPRK threat actors launch spear phishing attacks where the entire objective was to get the victim to install a browser extension vs. it being a post exploitation mechanism for persistence and data theft.” In its current incarnation, the malware works only on Windows, but Adair said there’s no reason it couldn’t be broadened to infect browsers running on macOS or Linux, too.
The blog post added: “Volexity’s own visibility shows the extension has been quite successful, as logs obtained by Volexity show the attacker was able to successfully steal thousands of emails from multiple victims through the malware’s deployment.”
Installing a browser extension during a phishing operation without the end-user noticing isn’t easy. SHARPEXT developers have clearly paid attention to research like what’s published here, here, and here, which shows how a security mechanism in the Chromium browser engine prevents malware from making changes to sensitive user settings. Each time a legitimate change is made, the browser takes a cryptographic hash of some of the code. At startup, the browser verifies the hashes, and if any of them don’t match, the browser requests the old settings to be restored.
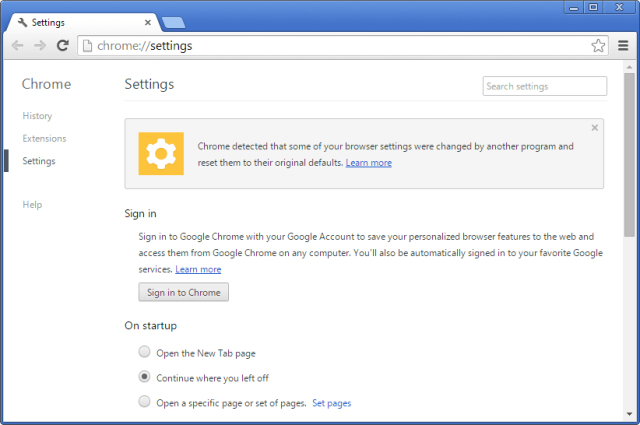
For attackers to work around this protection, they must first extract the following from the computer they’re compromising:
- A copy of the resources.pak file from the browser (which contains the HMAC seed used by Chrome)
- The user’s S-ID value
- The original Preferences and Secure Preferences files from the user’s system
After modifying the preference files, SHARPEXT automatically loads the extension and executes a PowerShell script that enables DevTools, a setting that allows the browser to run customized code and settings.
“The script runs in an infinite loop checking for processes associated with the targeted browsers,” Volexity explained. “If any targeted browsers are found running, the script checks the title of the tab for a specific keyword (for example ‘05101190,’ or ‘Tab+’ depending on the SHARPEXT version). The specific keyword is inserted into the title by the malicious extension when an active tab changes or when a page is loaded.”
Volexity
The post continued:
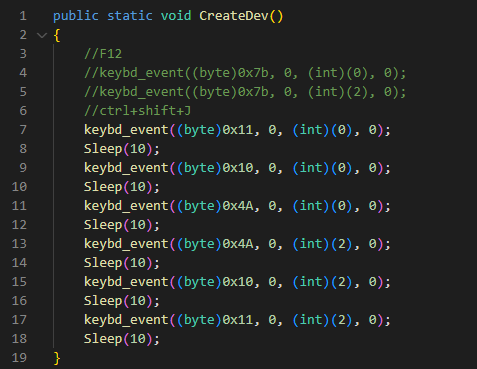
The keystrokes sent are equivalent to
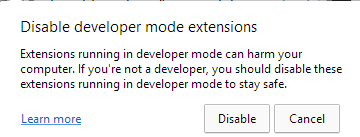
Control+Shift+J, the shortcut to enable the DevTools panel. Finally, the PowerShell script hides the newly opened DevTools window by using the ShowWindow() API and theSW_HIDEflag. At the end of this process, DevTools is enabled on the active tab, but the window is hidden.In addition, this script is used to hide any windows that could alert the victim. Microsoft Edge, for example, periodically displays a warning message to the user (Figure 5) if extensions are running in developer mode. The script constantly checks if this window appears and hides it by using the
ShowWindow()and theSW_HIDEflag.
Volexity
Once installed, the extension can perform the following requests:
| HTTP POST Data | Description |
| mode=list | List previously collected email from the victim to ensure duplicates are not uploaded. This list is continuously updated as SHARPEXT executes. |
| mode=domain | List email domains with which the victim has previously communicated. This list is continuously updated as SHARPEXT executes. |
| mode=black | Collect a blacklist of email senders that should be ignored when collecting email from the victim. |
| mode=newD&d=[data] | Add a domain to the list of all domains viewed by the victim. |
| mode=attach&name=[data]&idx=[data]&body=[data] | Upload a new attachment to the remote server. |
| mode=new&mid=[data]&mbody=[data] | Upload Gmail data to the remote server. |
| mode=attlist | Commented by the attacker; receive an attachments list to be exfiltrated. |
| mode=new_aol&mid=[data]&mbody=[data] | Upload AOL data to the remote server. |
SHARPEXT allows the hackers to create lists of email addresses to ignore and to keep track of emails or attachments that have already been stolen.
Volexity created the following summary of the orchestration of the various SHARPEXT components it analyzed:
Volexity
The blog post provides images, file names, and other indicators that trained people can use to determine if they have been targeted or infected by this malware. The company warned that the threat it poses has grown over time and isn’t likely to go away anytime soon.
“When Volexity first encountered SHARPEXT, it seemed to be a tool in early development containing numerous bugs, an indication the tool was immature,” the company said. “The latest updates and ongoing maintenance demonstrate the attacker is achieving its goals, finding value in continuing to refine it.”